How safe are your secrets? If you used Amazon’s Elastic Block Storage snapshots, you might want to check your settings.
New research just presented at the Def Con security conference reveals how companies, startups and governments are inadvertently leaking their own files from the cloud.
You may have heard of exposed S3 buckets — those Amazon-hosted storage servers packed with customer data but often misconfigured and inadvertently set to “public” for anyone to access. But you may not have heard about exposed EBS snapshots, which poses as much, if not a greater, risk.
These elastic block storage (EBS) snapshots are the “keys to the kingdom,” said Ben Morris, a senior security analyst at cybersecurity firm Bishop Fox, in a call with TechCrunch ahead of his Def Con talk. EBS snapshots store all the data for cloud applications. “They have the secret keys to your applications and they have database access to your customers’ information,” he said.
“When you get rid of the hard disk for your computer, you know, you usually shredded or wipe it completely,” he said. “But these public EBS volumes are just left for anyone to take and start poking at.”
He said that all too often cloud admins don’t choose the correct configuration settings, leaving EBS snapshots inadvertently public and unencrypted. “That means anyone on the internet can download your hard disk and boot it up, attach it to a machine they control, and then start rifling through the disk to look for any kind of secrets,” he said.
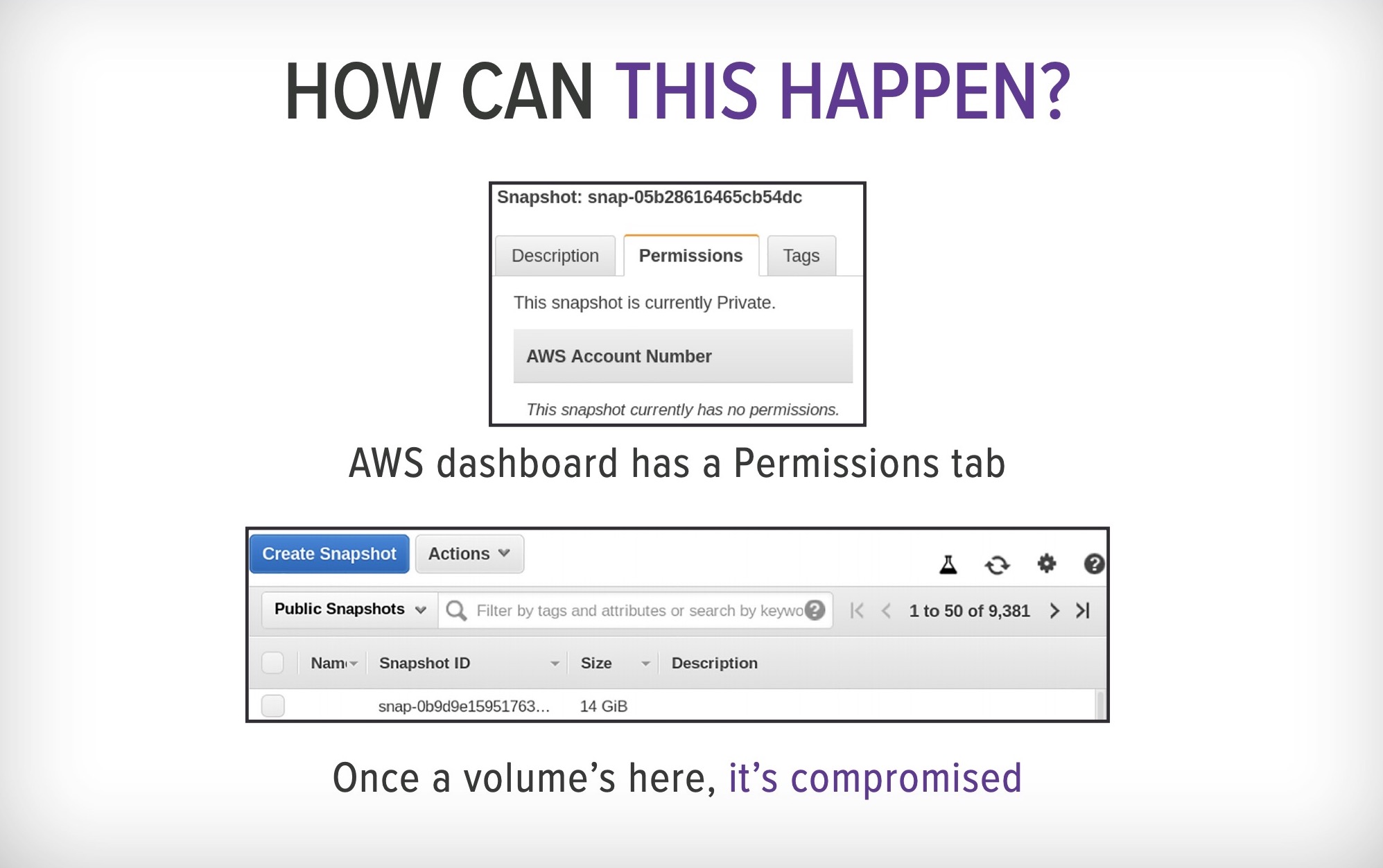
One of Morris’ Def Con slides explaining how EBS snapshots can be exposed. (Image: Ben Morris/Bishop Fox; supplied)
Morris built a tool using Amazon’s own internal search feature to query and scrape publicly exposed EBS snapshots, then attach it, make a copy and list the contents of the volume on his system.
“If you expose the disk for even just a couple of minutes, our system will pick it up and make a copy of it,” he said.
https://techcrunch.com/2019/08/09/aws-ebs-cloud-backups-leak/