Many popular iPhone apps secretly record your screen without asking
Many major companies, like Air Canada, Hollister and Expedia, are recording every tap and swipe you make on their iPhone apps. In most cases you won’t even realize it. And they don’t need to ask for permission.
You can assume that most apps are collecting data on you. Some even monetize your data without your knowledge. But TechCrunch has found several popular iPhone apps, from hoteliers, travel sites, airlines, cell phone carriers, banks and financiers, that don’t ask or make it clear — if at all — that they know exactly how you’re using their apps.
Worse, even though these apps are meant to mask certain fields, some inadvertently expose sensitive data.
Apps like Abercrombie & Fitch, Hotels.com and Singapore Airlines also use Glassbox, a customer experience analytics firm, one of a handful of companies that allows developers to embed “session replay” technology into their apps. These session replays let app developers record the screen and play them back to see how its users interacted with the app to figure out if something didn’t work or if there was an error. Every tap, button push and keyboard entry is recorded — effectively screenshotted — and sent back to the app developers.
Or, as Glassbox said in a recent tweet: “Imagine if your website or mobile app could see exactly what your customers do in real time, and why they did it?”
The App Analyst, a mobile expert who writes about his analyses of popular apps on his eponymous blog, recently found Air Canada’s iPhone app wasn’t properly masking the session replays when they were sent, exposing passport numbers and credit card data in each replay session. Just weeks earlier, Air Canada said its app had a data breach, exposing 20,000 profiles.
“This gives Air Canada employees — and anyone else capable of accessing the screenshot database — to see unencrypted credit card and password information,” he told TechCrunch.
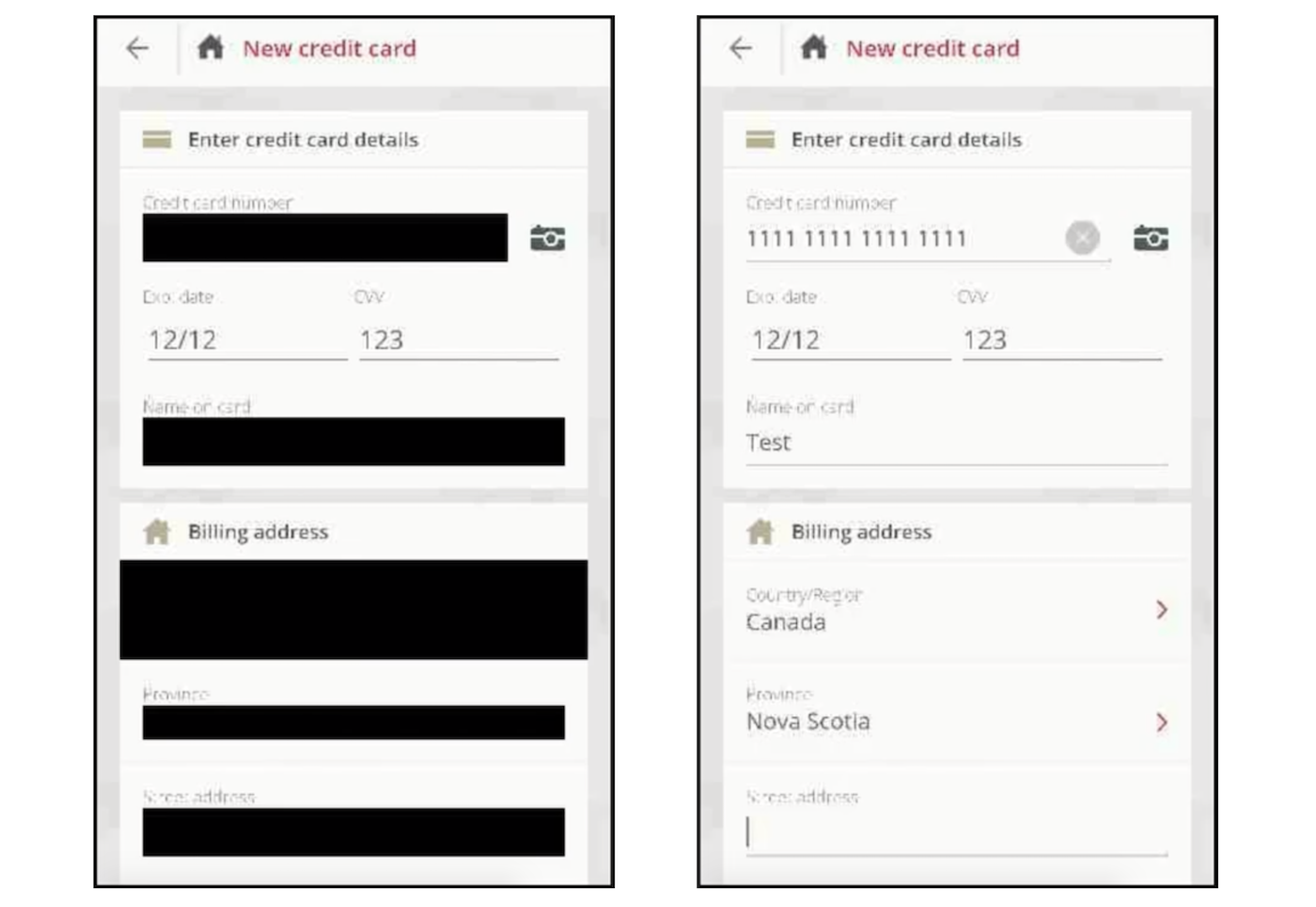
In the case of Air Canada’s app, although the fields are masked, the masking didn’t always stick (Image: The App Analyst/supplied)
Big Telecom Sold Highly Sensitive Customer GPS Data Typically Used for 911 Calls
A Motherboard investigation has found that around 250 bounty hunters and related businesses had access to AT&T, T-Mobile, and Sprint customer location data.
Around 250 bounty hunters and related businesses had access to AT&T, T-Mobile, and Sprint customer location data, according to documents obtained by Motherboard. The documents also show that telecom companies sold data intended to be used by 911 operators and first responders to data aggregators, who sold it to bounty hunters. The data was in some cases so accurate that a user could be tracked to specific spots inside a building.
The news shows not only how widely Americans’ sensitive location data has been sold through the overlooked and questionable data broker market, but also how the ease-of-access dramatically increased the risk of abuse. Motherboard found that an individual company made more than 18,000 data location requests through a data broker; other companies made thousands of requests. The full details of our investigation are available here.
“This scandal keeps getting worse. Carriers assured customers location tracking abuses were isolated incidents. Now it appears that hundreds of people could track our phones, and they were doing it for years before anyone at the wireless companies took action,” Oregon Senator Ron Wyden said in an emailed statement after presented with Motherboard’s findings. “That’s more than an oversight—that’s flagrant, wilful disregard for the safety and security of Americans.”