via arstechnica:
China Telecom, the large international communications carrier with close ties to the Chinese government, misdirected big chunks of Internet traffic through a roundabout path that threatened the security and integrity of data passing between various providers’ backbones for two and a half years, a security expert said Monday. It remained unclear if the highly circuitous paths were intentional hijackings of the Internet’s Border Gateway Protocol or were caused by accidental mishandling.
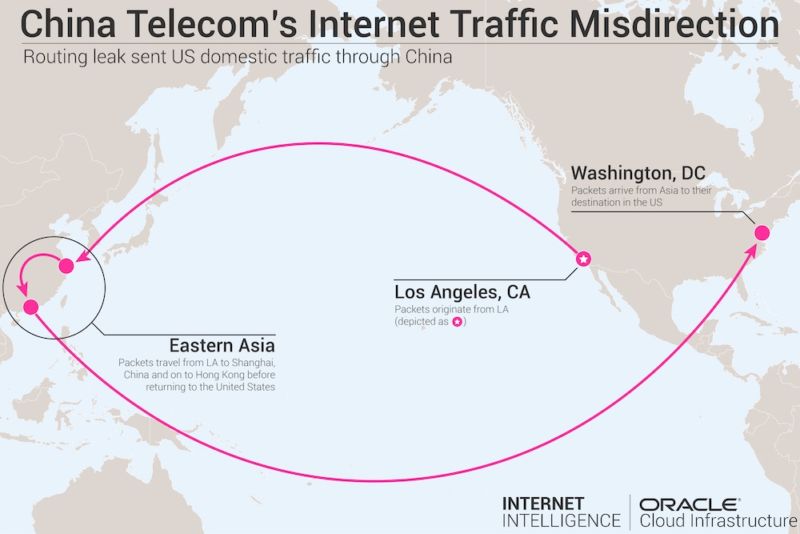
For almost a week late last year, the improper routing caused some US domestic Internet communications to be diverted to mainland China before reaching their intended destination, Doug Madory, a researcher specializing in the security of the Internet’s global BGP routing system, told Ars. As the following traceroute from December 3, 2017 shows, traffic originating in Los Angeles first passed through a China Telecom facility in Hangzhou, China, before reaching its final stop in Washington, DC. The problematic route, which is visualized in the graphic above, was the result of China Telecom inserting itself into the inbound path of Verizon Asian Pacific.
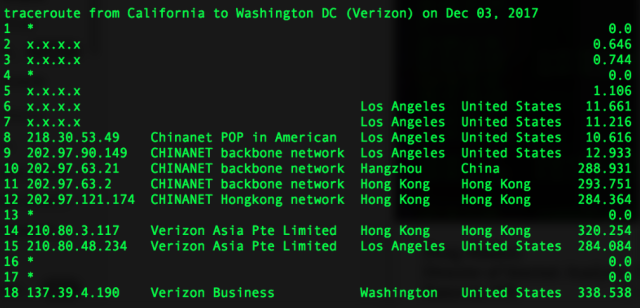
The routing snafu involving domestic US Internet traffic coincided with a larger misdirection that started in late 2015 and lasted for about two and a half years, Madory said in a blog post published Monday. The misdirection was the result of AS4134, the autonomous system belonging to China Telecom, incorrectly handling the routing announcements of AS703, Verizon’s Asia-Pacific AS. The mishandled routing announcements caused several international carriers—including Telia’s AS1299, Tata’s AS6453, GTT’s AS3257, and Vodafone’s AS1273—to send data destined for Verizon Asia-Pacific through China Telecom, rather than using the normal multinational telecoms.
For the next 30 months or so, a large amount of traffic that used Verizon’s AS703 improperly passed through AS4134 in mainland China first. The circuitous route is reflected in the following traceroute taken on May 1, 2017:
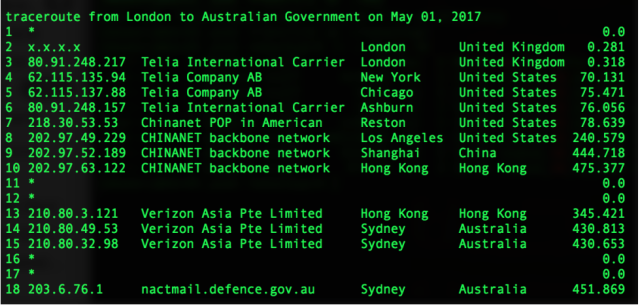
“On average I believe we saw as much as 20 percent of our BGP sources carrying these routes at any given time,” Madory told Ars. “It isn’t the same as saying 20 percent of the Internet, but it is safe to say that a significant minority of the Internet was carrying these routes.”
BGP fragility
The sustained misdirection further underscores the fragility of BGP, which forms the underpinning of the Internet’s global routing system. In April, unknown attackers used BGP hijacking to redirect traffic destined for Amazon’s Route 53 domain-resolution service. The two-hour event allowed the attackers to steal about $150,000 in digital coins as unwitting people were routed to a fake MyEtherWallet.com site rather than the authentic wallet service that got called normally. When end users clicked through a message warning of a self-signed certificate, the fake site drained their digital wallets.
In 2013, malicious hackers repeatedly hijacked massive chucks of Internet traffic in what was likely a test run. Also in 2013, spyware service provider Hacking Team orchestrated the hijacking of IP addresses it didn’t own to help Italian police regain control over several computers they were monitoring in an investigation. A year later, domestic Russian Internet traffic was diverted through China.
On two occasions last year, traffic to and from major US companies was suspiciously and intentionally routed through Russian service providers. Traffic for Visa, MasterCard, and Symantec—among others—was rerouted in the first incident in April, while Google, Facebook, Apple, and Microsoft traffic was affected in a separate BGP event about eight months later.
By routing traffic through networks controlled by the attacker, BGP manipulation allows the adversary to monitor, corrupt, or modify any data that’s not encrypted. Even when data is encrypted, attacks with names such as DROWN or Logjam have raised the specter that some of the encrypted data may have been decrypted. Even when encryption can’t be defeated, attackers can sometimes trick targets into dropping their defenses, as the BGP hijacking against MyEtherWallet.com did.
h/t GR