US Universities And Retirees Are Funding The Technology Behind China’s Surveillance State
Millions of dollars from US university endowments, foundations, and retirement plans have helped fund two billion-dollar Chinese facial recognition startups: SenseTime and Megvii. The Chinese government is using their technologies to surveil and profile its own citizens.
HONG KONG — Princeton University and the US’s largest public pension plan are among a number of stateside organizations funding technology behind the Chinese government’s unprecedented surveillance of some 11 million people of Muslim ethnic minorities.
Since 2017, Chinese authorities have detained more than a million Uighur Muslims and other ethnic minorities in political reeducation camps in the country’s northwest region of Xinjiang, identifying them, in part, with facial recognition software created by two companies: SenseTime, based in Hong Kong, and Beijing’s Megvii. A BuzzFeed News investigation has found that US universities, private foundations, and retirement funds entrusted their money to investors that, in turn, plowed hundreds of millions of dollars into these two startups over the last three years. Using that capital, SenseTime and Megvii have grown into billion-dollar industry leaders, partnering with government agencies and other private companies to develop tools for the Communist Party’s social control of its citizens.
Also among the diverse group of institutions helping to finance China’s surveillance state: the Alaska Retirement Management Board, the Massachusetts Institute of Technology, and the Rockefeller Foundation all of which are “limited partners” in private equity funds that invested in SenseTime or Megvii. And even as congressional leaders, such as Sen. Marco Rubio of Florida, have championed a bill to condemn human rights abuses in Xinjiang, their own states’ public employee pension funds are invested in companies building out the Chinese government’s system for tracking Uighurs.
“The story here is why private equity firms and venture capitalists are aiding the government of China, which has a history of surveilling and curtailing behavior deemed inappropriate to the goals of the Communist Party,” said one US-based technology investor, who declined to be named for fear of ruining business relationships. Being a limited partner is “not an excuse” for ignorance, he added, noting that any organization deploying millions of dollars should bear some of that responsibility.
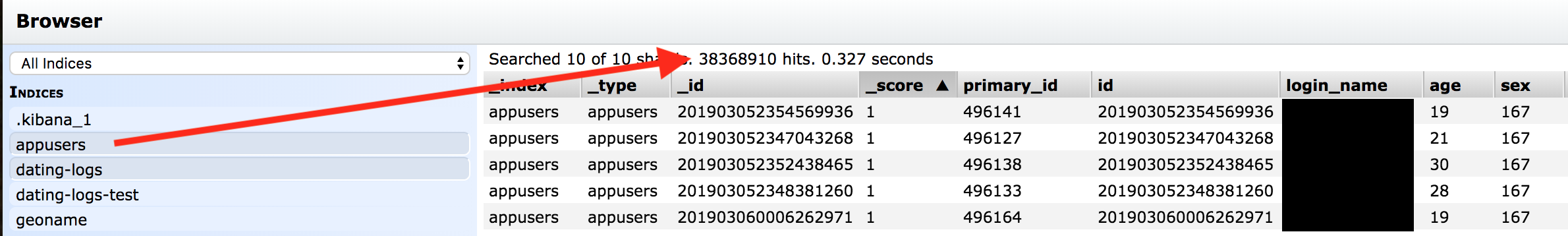
Chinese Dating Apps Targeting Americans Expose 42.5 Million Records Online

On May 25th I discovered a non password protected Elastic database that was clearly associated with dating apps based on the names of the folders. The IP address is located on a US server and a majority of the users appear to be Americans based on their user IP and geolocations. I also noticed Chinese text inside the database with commands such as:
- 模型更新完成事件已触发,同步用户到
- according to Google Translate: The model update completion event has been triggered, syncing to the user.
The strange thing about this discovery was that there were multiple dating applications all storing data inside this database. Upon further investigation I was able to identify dating apps available online with the same names as those in the database. What really struck me as odd was that despite all of them using the same database, they claim to be developed by separate companies or individuals that do not seem to match up with each other. The Whois registration for one of the sites uses what appears to be a fake address and phone number. Several of the other sites are registered private and the only way to contact them is through the app (once it is installed on your device).
Finding several of the users’ real identity was easy and only took a few seconds to validate them. The dating applications logged and stored the user’s IP address, age, location, and user names. Like most people your online persona or user name is usually well crafted over time and serves as a unique cyber fingerprint. Just like a good password many people use it again and again across multiple platforms and services. This makes it extremely easy for someone to find and identify you with very little information. Nearly each unique username I checked appeared on multiple dating sites, forums, and other public places. The IP and geolocation stored in the database confirmed the location the user put in their other profiles using the same username or login ID.